Our research team has put together all of the most relevant news topics in the Ransomware and IoT security fields, as well as their impacts and their expert recommendations:
IT
Bumblebee Malware Loader
Description: A new malware loader, Bumblebee, is being used as a replacement for the BazarLoader and IcedID to deliver ransomware payloads. Phishing campaigns were observed in which threat actors used Bumblebee to drop shellcode and the Cobalt Strike, Sliver, and Meterpreter frameworks.
Attack Parameters: The campaigns are delivered via phishing emails containing a link to a malicious file. For persistence, the malware uses scheduled tasks and WMI execution.
Many similarities were found between the loader and TrickBot, including the web-inject module and the evasion technique.
Impact: As BazarLoader was used in attacks in the past, Bumblebee is likely to become a popular tool for ransomware groups.
Recommendations: Following are best practices recommendations to minimize the chances of being infected by ransomware:
- Apply the latest security patches on the assets in the network.
- Use unique passwords and multi-factor authentication on authentication paths to OT assets.
- Educate staff about the risks and methods of ransomware attacks and how to avoid infection.
SCADAfence Coverage: The SCADAfence Platform detects new connections, connections to and from external devices, and connections to and from the Internet. The platform also detects suspicious behavior based on IP reputation, hash reputation, and domain reputation.
The SCADAfence Platform also detects scheduled tasks and WMI process creation, as well as the use of Cobalt Strike and Meterpreter.
Ransomware
Lapsus$ Extortion Group – T-Mobile Breach
Description: Lapsus$ group breached T-Mobile’s network using stolen VPN credentials and gained access to internal systems. The stolen credentials, found on illicit platforms, allowed the attackers to access the company’s internal tools, which allowed them to conduct sim-swapping attacks.
The credentials used in the hack were disabled after discovering the breach.
Attack Parameters: Lapsus$ compromises systems to steal source code, customer lists, databases, and other valuable data, then attempts to extort the victim with ransom demands that threaten to publicly leak the data. They primarily focus on obtaining compromised credentials for initial access using the following methods:
- Deploying Redline password stealer to obtain passwords and session tokens.
- Buying credentials and session tokens on criminal underground forums.
- Paying employees at targeted organizations for access to credentials and MFA approval.
- Searching public code repositories for exposed credentials.
- The group also uses RDP and VDI to remotely access a business’ environment.
Impact: No sensitive customer data was stolen.
Recommendations: Following are best practices recommendations:
- Make sure secure offline backups of critical systems are available and up-to-date.
- Apply the latest security patches on the assets in the network.
- Use unique passwords and multi-factor authentication on authentication paths to OT assets.
- Encrypt sensitive data when possible.
- Educate staff about the risks and methods of ransomware attacks and how to avoid infection.
SCADAfence Coverage: The SCADAfence Platform detects new connections, connections to and from external devices, and connections to and from the Internet. The platform also detects suspicious behavior based on IP reputation, hash reputation, and domain reputation.
RDP connections can be tracked with the User Activity Analyzer.
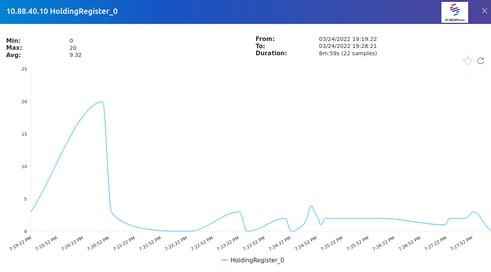 SCADAfence Platform - User Activity Analyzer
SCADAfence Platform - User Activity Analyzer
Black Basta Ransomware
Description: A new ransomware operation, Black Basta, uses a double-extortion scheme, where the threat actors demand a ransom to receive a decryptor and prevent the publishing of the victim's stolen data.
Targets: Among the operation’s victims are the American Dental Association (ADA) and the German wind turbine giant Deutsche Windtechnik.
Attack Parameters: The malware requires administrator privileges to work, and hijacks the Windows Fax service for persistence on the infected systems. Similarities were found between Black Basta and Conti.
Impact: The ADA took affected systems offline, which disrupted various online services, telephones, email, and webchat.
Deutsche Windtechnik switched off the remote data monitoring connections to the wind turbines, but claimed the wind turbines did not suffer any damage.
Recommendations: Following are best practices recommendations:
- Make sure secure offline backups of critical systems are available and up-to-date.
- Apply the latest security patches on the assets in the network.
- Use unique passwords and multi-factor authentication on authentication paths to OT assets.
- Encrypt sensitive data when possible.
- Educate staff about the risks and methods of ransomware attacks and how to avoid infection.
SCADAfence Coverage: The SCADAfence Platform detects new connections, connections to and from external devices, and connections to and from the Internet. The platform also detects suspicious behavior based on IP reputation, hash reputation, and domain reputation.
Stormous – Coca-Cola Breach
Description: Stormous gang claimed it has successfully breached some of Coca-Cola’s servers and stole over 160GB of data. There is no indication that Stormous deployed file-encrypting malware on their victims’ networks, making them closer to a data extortion group, than a ransomware group.
Attack Parameters: The group works with the tactic of double extortion, which is encryption and data theft. The stolen files are leaked if the victim does not pay the ransom.
Impact: Among the files listed, there are compressed documents, text files with admin, emails, and passwords, account and payment ZIP archives, and other types of sensitive information.
Recommendation: Following are best practices recommendations:
- Make sure secure offline backups of critical systems are available and up-to-date.
- Apply the latest security patches on the assets in the network.
- Use unique passwords and multi-factor authentication on authentication paths to OT assets.
- Encrypt sensitive data when possible.
- Educate staff about the risks and methods of ransomware attacks and how to avoid infection.
SCADAfence Coverage: The SCADAfence Platform detects new connections, connections to and from external devices, and connections to and from the Internet. The platform also detects suspicious behavior based on IP reputation, hash reputation, and domain reputation.
IoT
DNS Vulnerability in uClibc IoT Library (CVE-2022-30295)
Description: A new vulnerability affecting the DNS implementation of all versions of uClibc and uClibc-ng (CVE-2022-30295). This could allow an attacker to mount DNS poisoning attacks against IoT devices and routers to potentially take control of them.
Affected vendors: Both uClibc and uClibc-ng are widely used by vendors such as Netgear, Axis, and Linksys, as well as Linux distributions.
Attack Parameters: The vulnerability is caused by the predictability of transaction IDs included in the DNS requests, which may allow attackers to perform DNS poisoning attacks.
Impact: Successful exploitation could allow an attacker to alter or intercept network traffic to compromise connected devices.
This vulnerability has a broad scope not only because of the devices it potentially affects, but also because of the inherent importance of DNS to any device connecting over IP.
Recommendations: An official patch or workarounds have not yet been released.
SCADAfence Coverage: The SCADAfence Platform detects new connections, connections to and from external devices, and connections to and from the Internet. The platform also detects suspicious behavior based on IP reputation, hash reputation, and domain reputation.
DNS connections can be tracked with User Activity Analyzer.


